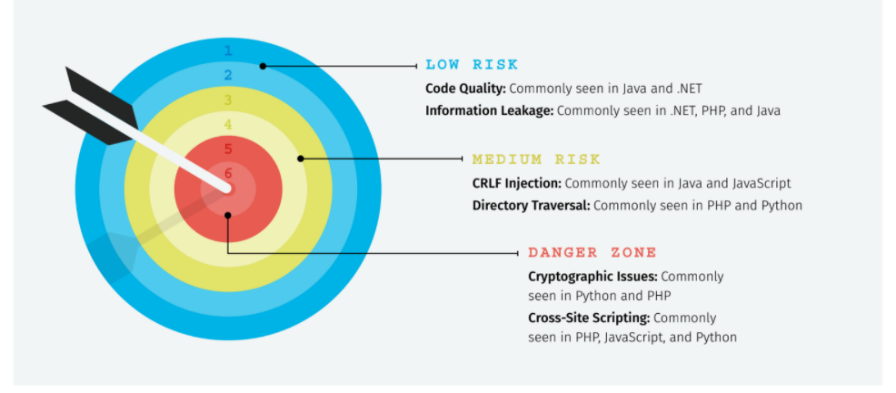
Modern software development is full of security risk. Factors like lingering security debt, insecure open source libraries, and irregular scanning cadences can all impact how many flaws dawdle in your code, leading to higher rates of dangerous bugs in susceptible and popular languages. For example, we know from State of Software Security v11 that PHP has a high rate (nearly 75 percent) of cross-site scripting flaws on initial scan, which is also the most common type of open source code vulnerability across nearly every language. It’s a dangerous one.
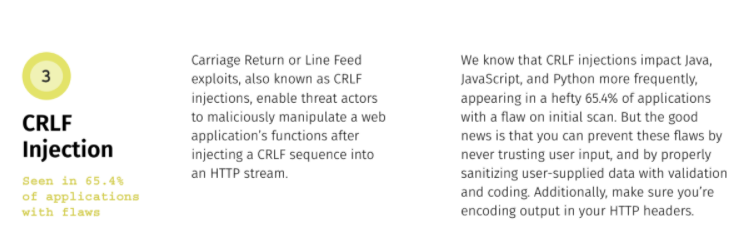
CRLF injection – which is commonly seen in Java and JavaScript – can lead to maliciously manipulated web applications if a threat actor is able to inject a CRLF sequence into an HTTP stream. CRLF injection is dangerous and appears in a sizeable 65 percent of applications with a flaw on initial scan, posing a decent risk to apps written in Java and JavaScript if left unchecked.
But not all flaws are so high-risk for common languages; Information Leakage, for example, is most often seen in .NET, PHP, and Java, typically stemming from a lack of secure code training. To stay one step ahead of even the low-risk (and high-risk) flaws, developers need to be armed with the right knowledge and tools so that they can produce more secure code to reduce the chance of a breach – whether low risk or in the danger zone.
Understanding how flaws impact programming languages across the board is crucial to preventing them. Take note of which languages tend to carry the most high-risk flaws first; whether or not yours in the mix, it’s a good idea to brush up on secure coding best practices and try your hand at hacking and patching real applications with Veracode Security Labs.
You can’t fake it when it comes to security: hands-on-keyboard education is critical to jumping these (and other) hurdles as you create innovative applications. If you want to keep data safe and squash these risky bugs, you have to think like an attacker and avoid flaw-filled curveballs in the future.
To learn more about which vulnerabilities are in the danger zone (and how to go about preventing them), check out our infosheet here.