Fix resources hub
Save time
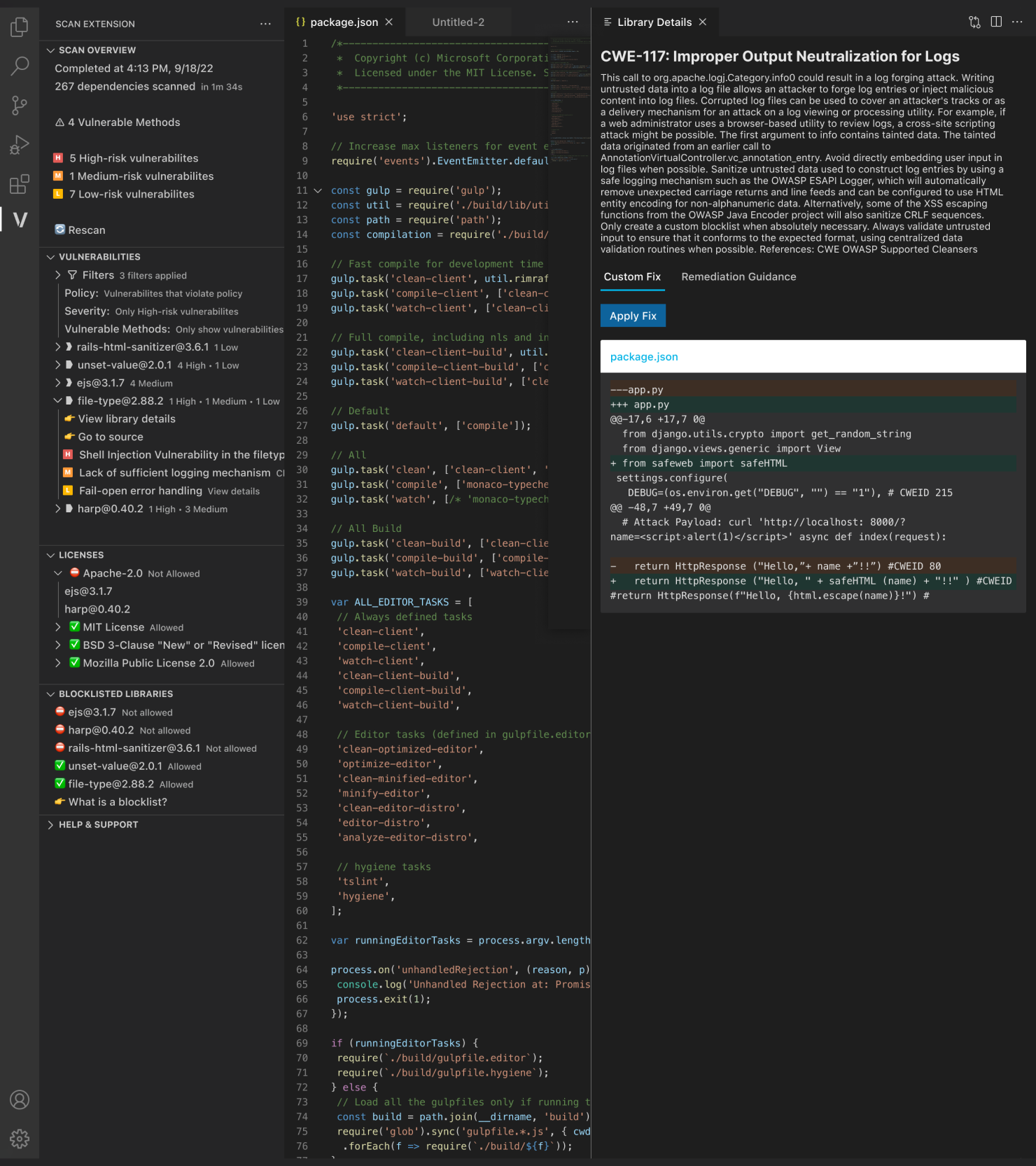
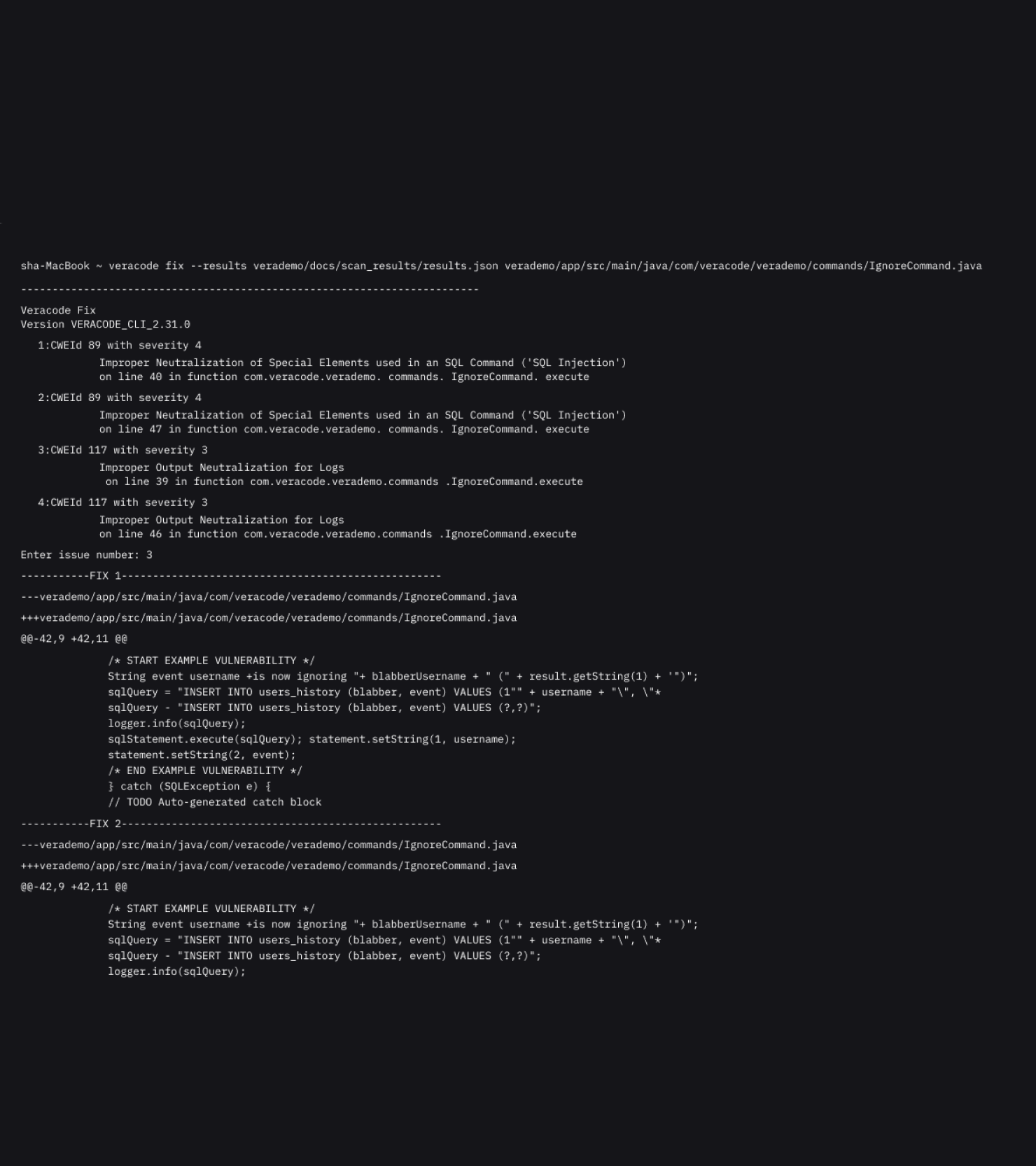
Get solutions for common flaws in seconds.
Secure more
Coverage for the most common flaws across ten popular languages.
Reduce churn
Give developers time back from fixing repetitive flaws.
Responsible, reliable, comprehensive
Veracode Fix is the AI security assistant you can trust
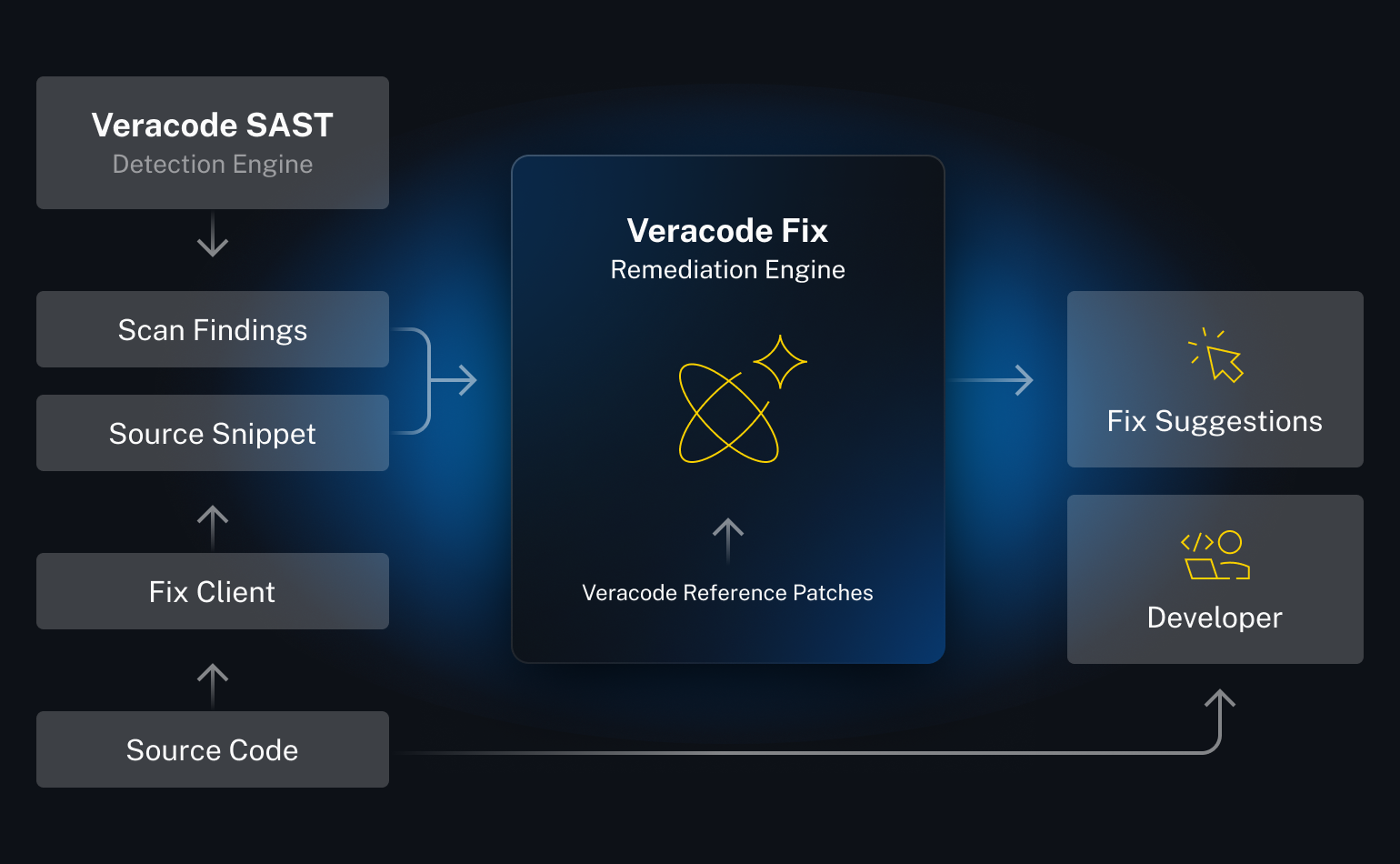
The unique design of Veracode Fix keeps developers and Veracode Experts in control. Reliable solutions, scaled with Generative AI.
Hallucination-free solutions
Responsible-by-design architecture delivers consistent solutions based on human expertise.
Inbuilt quality-gates
All suggestions pass strict quality gates, building confidence and trust
Huge language support
Veracode Fix supports more languages, frameworks, and flaws than anyone.
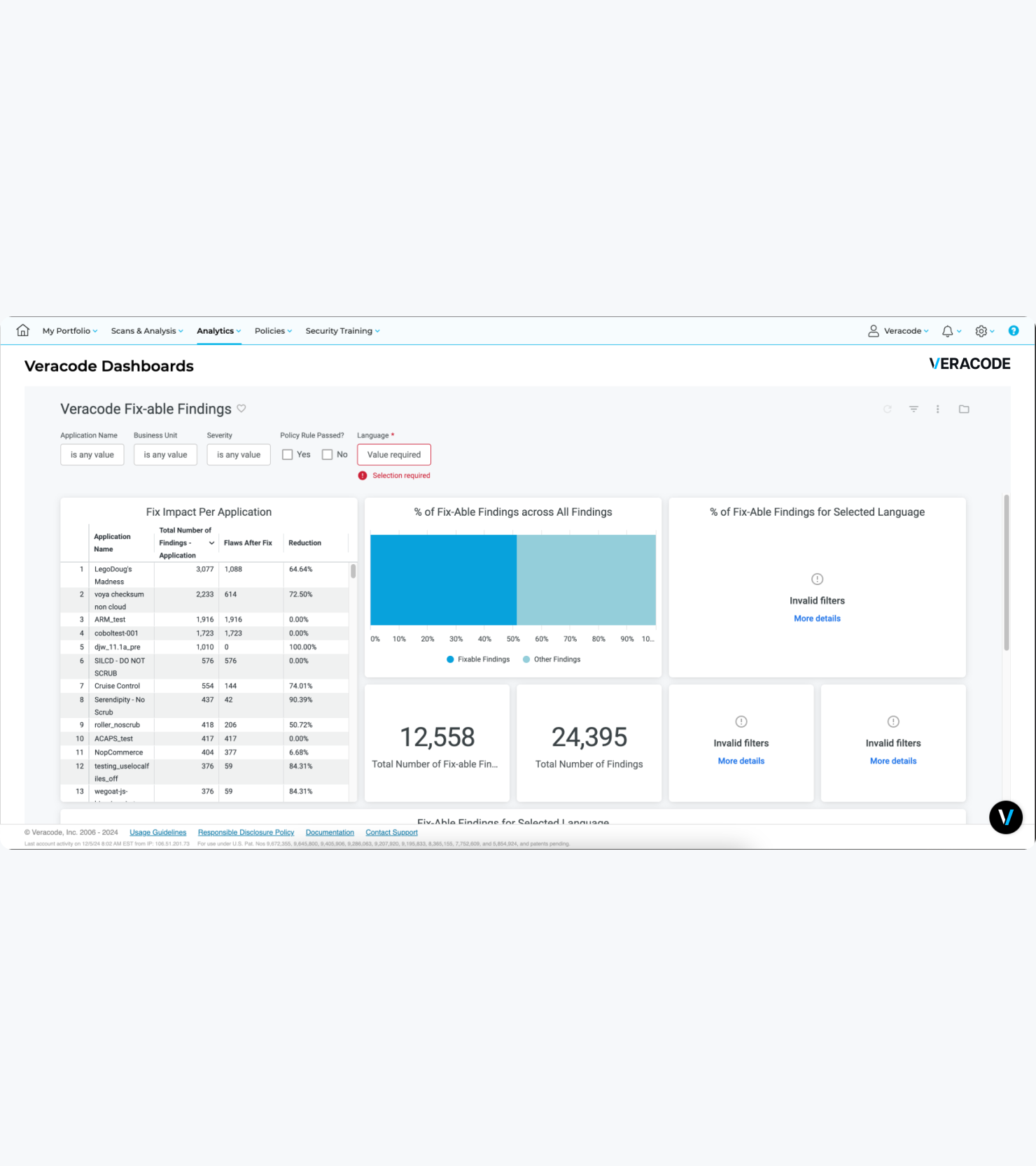
Secure your code in seconds with AI-generated fixes
Automate security flaw remediation, significantly reduce the time and effort required to fix vulnerabilities, and enhance the overall security posture.
Veracode Fix and the future of intelligent software security
Using artificial intelligence to help organizations defend against application security threats with speed, accuracy, and efficiency.

Get started today
Harness the Power of Veracode
For secure, confident coding to identify
and fix vulnerabilities early.